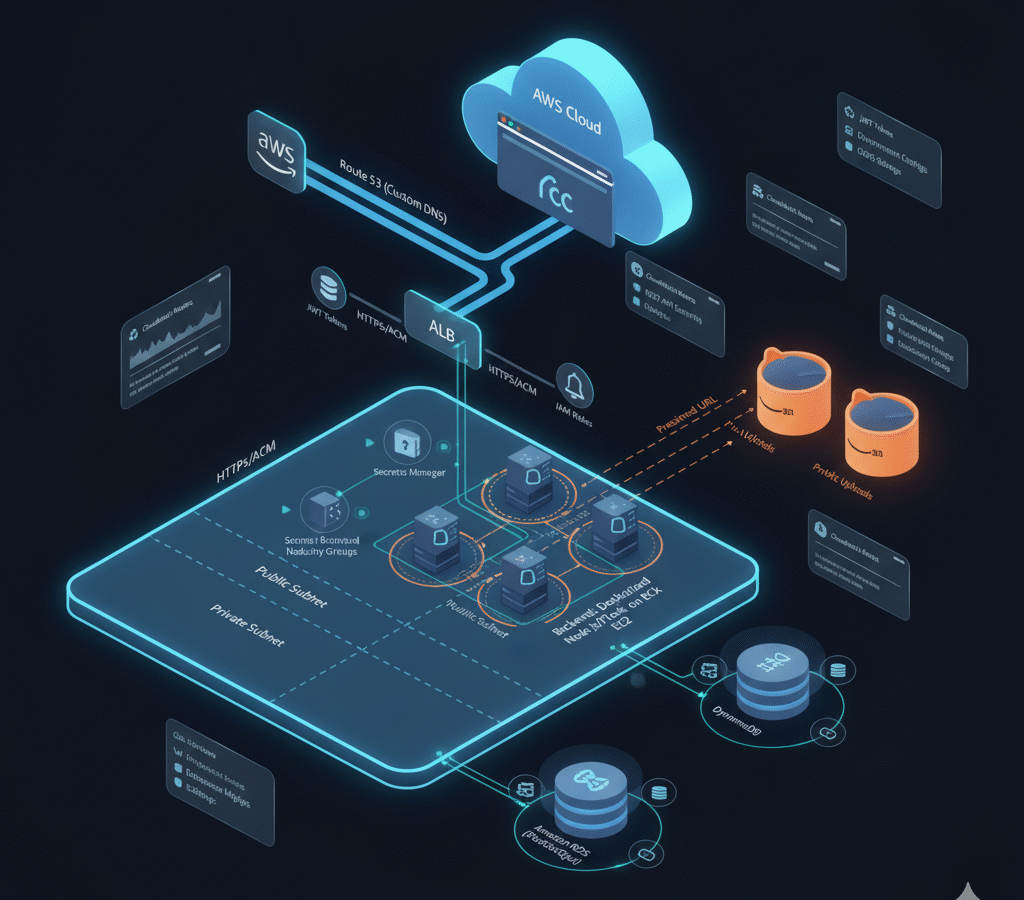
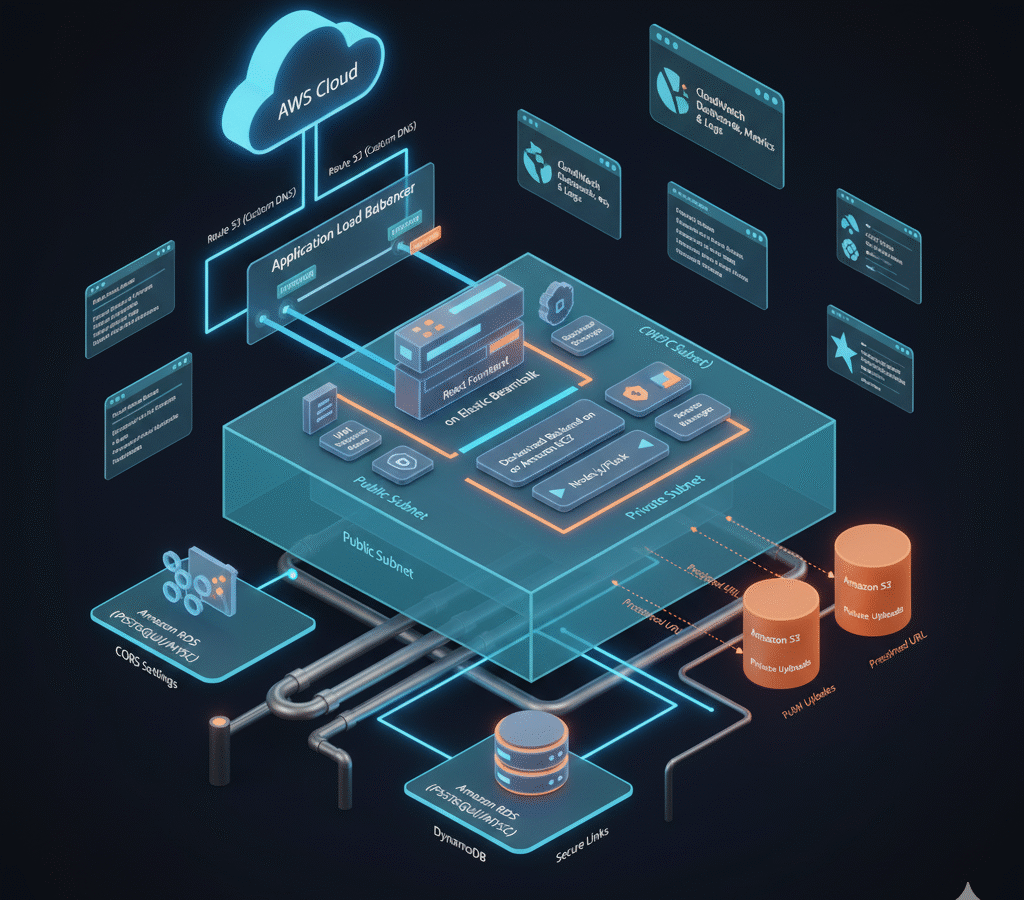
A cloud-native web application deployed on AWS with independently deployable tiers: a React frontend on Elastic Beanstalk and a Dockerized backend (e.g., Node/Flask/Django) on Amazon EC2 inside a VPC. Data is persisted in Amazon RDS (MySQL/PostgreSQL) or DynamoDB, with file/image uploads to Amazon S3 using presigned URLs and separate public/private paths. Security is enforced with least-privilege IAM roles/policies, tightly scoped Security Groups, and HTTPS via ACM (optionally fronted by a load balancer and Route 53 custom domain).
The deployment offers features such:
- User authentication (JWT/session) and CRUD APIs for primary entities, consumed by a SPA via REST with CORS and environment-based configs.
- Database layer on RDS or DynamoDB with schemas/migrations, snapshots/backups, and parameterized connections.
- S3 media pipeline with presigned uploads/downloads, lifecycle rules, and clear separation of public vs. private objects.
- VPC design with public/private subnets, NAT where needed, and Security Groups exposing only necessary ports.
- IAM roles/policies granting EC2 least-privilege access to S3 and DB; secrets via Parameter Store/Secrets Manager.
- HTTPS everywhere using ACM certificates and HTTP→HTTPS redirects; optional Route 53 for DNS and subdomain routing.
- Observability with CloudWatch logs/metrics/alarms and structured app logging for audits and incident response.
- Documentation & deliverables: GitHub repo, deployment guide (README), live frontend/backend URLs, architecture diagram PDF, and IAM/security screenshots.
React SPA on Elastic Beanstalk + Dockerized API on EC2 within a VPC, with RDS/DynamoDB for data and S3 presigned uploads for media. Least-privilege IAM roles, tight Security Groups, and ACM-backed HTTPS secure public endpoints; CloudWatch provides logs, metrics, and alarms. Optional Route 53 domain, environment-based configs, and a README + architecture diagram make the stack reproducible and production-ready.